
Apple continues to ignore the most dangerous iPhone vulnerability: everyone can be hacked
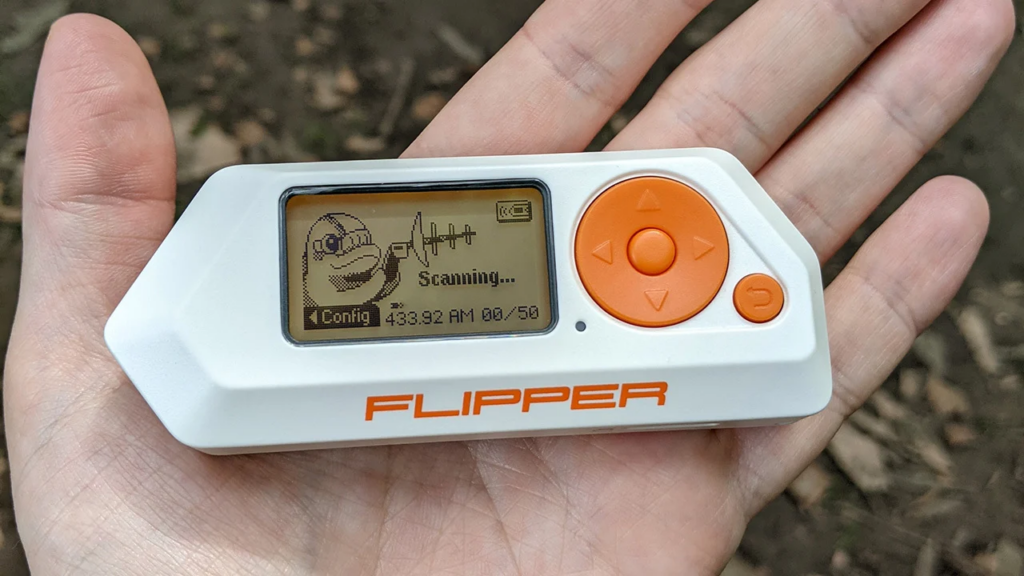
Back in September, 9to5Mac reported that enthusiasts managed to hack several iPhones and iPads using a popular hacker’s “tamagotchi” device called Flipper Zero, but Apple has not yet attempted to fix the vulnerability in its gadgets.
With the help of Flipper Zero, hackers can connect to an iPhone or iPad via Bluetooth to send a lot of requests to the device, which eventually disables the gadget (DoS attacks). Moreover, along with ADV packages, attackers can send files to a smartphone. Despite the fact that the vulnerability was present in iOS 16, the developers did not fix it even in the beta version of iOS 17.2.
The attack exploits a Bluetooth Low-Energy (BLE) pairing sequence vulnerability that Apple will leverage in its ecosystem to power AirDrop, HandOff, iBeacon, HomeKit, and Apple Watch connectivity. The main feature of BLE is its ability to send advertising packets or ADVs to identify local devices on iPhones and iPads. It is thanks to these packages that you see an animated window pop up when you connect AirPods.
It’s worth noting that the Flipper Zero’s range is limited to 50 meters, while the normal Bluetooth radio range is about 50 meters (~164 feet), so an attacker needs to be fairly close to the victim. However, ordinary attackers can use it in public places, such as cafes or events.
There’s no real way to protect your devices yet, but you can disable Bluetooth completely in iOS settings.

